Sunday, 23 April 2017
1
Sunday, 23 April 2017
1. Bitcoin
2. Dogecoin
3. Litecoin
4. Paycoin
Requirement
– Basic web programing
– Php 5 or beter
– You coin like wallet
– MySQL (phpmyadmin)
Features
– installation script (free guide e-book how to install)
– automatic payment
– rpc blockchain , bitcoinqt , litecoin and doge support
– accept bitcoin , litecoin , doge
– create fake transactions (not support litecoin)
– affiliates program (beta)
– custom time left
– custon price payment , change/stop payout
– add/dete/update time left
– transactions info (see on phpmyadmin)
– Detailed all coin earning
read more
Bitcoins Doubler Script on sale
bitcoin doubler
The script – doubler cryptocurrency. Full version 2016.
Supports 4 types of cryptocurrencies:1. Bitcoin
2. Dogecoin
3. Litecoin
4. Paycoin
Requirement
– Basic web programing
– Php 5 or beter
– You coin like wallet
– MySQL (phpmyadmin)
Features
– installation script (free guide e-book how to install)
– automatic payment
– rpc blockchain , bitcoinqt , litecoin and doge support
– accept bitcoin , litecoin , doge
– create fake transactions (not support litecoin)
– affiliates program (beta)
– custom time left
– custon price payment , change/stop payout
– add/dete/update time left
– transactions info (see on phpmyadmin)
– Detailed all coin earning
BUY NOW
Saturday, 7 November 2015
0
Saturday, 7 November 2015
read more
Protect your PC from ShortCut Virus!! 100% Working!!!
Step1: Bring Task Manager by pressing ‘Ctrl+Shift+Esc’
Step2: Select ‘Process’ Tab from the Task Manager
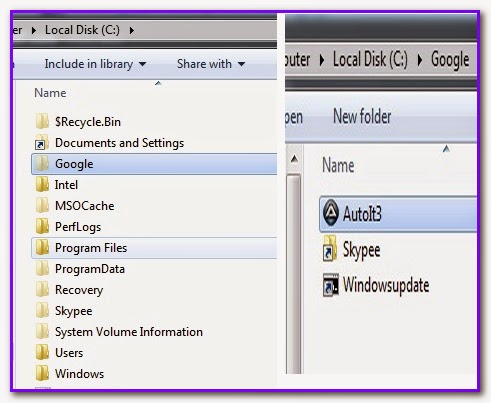
Step3: Find “AutoIt3” and select it. Then Press ‘End Process’ and select ‘End Now’
Step4: Now go to ‘Control Panel’ and Click ‘Folder Option’
Step5: From Folder Option’s ‘View’ tab Tick in to “Show Hidden Files” & Tick out to “Hide Protected Operating System Files”. Then click Apply and Ok.
Step6: Now go to C Drive & Delete the hidden folder named by “Google” & “Skypee”. Thus delete these 2 folders from every drive of your Hard Disk.
Step7: Now from start Menu, go to ‘Startup’ and Delete “GoogleUpdate” and “WindowsUpdate”
Final Step: Use Avast Antivirus and select “Boot Time Scan” or from any other antivirus scan your whole hard disk.
Step2: Select ‘Process’ Tab from the Task Manager
Step3: Find “AutoIt3” and select it. Then Press ‘End Process’ and select ‘End Now’
Step4: Now go to ‘Control Panel’ and Click ‘Folder Option’
Step5: From Folder Option’s ‘View’ tab Tick in to “Show Hidden Files” & Tick out to “Hide Protected Operating System Files”. Then click Apply and Ok.
Step6: Now go to C Drive & Delete the hidden folder named by “Google” & “Skypee”. Thus delete these 2 folders from every drive of your Hard Disk.
Step7: Now from start Menu, go to ‘Startup’ and Delete “GoogleUpdate” and “WindowsUpdate”
Final Step: Use Avast Antivirus and select “Boot Time Scan” or from any other antivirus scan your whole hard disk.
0
This key is for Avast Free Anti Virus. It will work all version of Avast Free Anti Virus software. This Key works till 2099!!
Official Site: https://www.avast.com/
How to Activate key:
>Fist Go to your Avast Anti virus's main interface
>Then Go to Settings
>Then Go to Registration
>Then select "Insert Registration Key"
>Then Put the key given below
>Then select ok.
read more
Avast 2015 Free Anti Virus License/Registration Key!!!
This key is for Avast Free Anti Virus. It will work all version of Avast Free Anti Virus software. This Key works till 2099!!
Official Site: https://www.avast.com/
How to Activate key:
>Fist Go to your Avast Anti virus's main interface
>Then Go to Settings
>Then Go to Registration
>Then select "Insert Registration Key"
>Then Put the key given below
>Then select ok.
Key:
C59249769E9900N1595-ENS7ULJH
Trick: If you want to use Avast Internet security full version with this key just follow my instruction.
- Install Avast free antivirus
- Activate Avast with that key
- then Install Avast Internet Security
0
read more
IObit Protected Folder V1.2.0 full with Key
0
read more
Tuneup Utility 2015 Product key
Official Details: http://www.tune-up.com/products/tuneup-utilities/features/
Download Link: http://www.tune-up.com/download/
Product key 1:
Use any of these Product Key for TuneUp Utilities 2015 Given Below:
CMETO-2KELO-T39DN-A32EW-FTX2L-FZEZU
CMNPD-UPYJQ-NUQU2-A4BPO-MPWMN-7DRNS
CMEMI-GTISN-W69OO-AMVUG-FM2TI-IPROJ
CMH2P-QXHY6-7HGX9-AFKPM-G2QBX-CZG64
CMGHG-3O24M-BHECP-QP3E4-HHGHR-OOLWW
CMBK3-6EKE6-ZC22B-AQE3D-AKXRG-R6AWP
CMHDF-TCPN7-V2P4E-QRF42-GD4TT-F9C9Q
CM2S6-7JX7V-I3MGR-Q27AM-3SBKV-AW7ZV
CMETO-2KELO-T39DN-A32EW-FTX2L-FZEZU
CMKRU-MS4LL-R7QNG-AGCCY-LR9SS-F6GIW
CM3G6-DR2R3-QOWZW-ATUEF-2GHSE-IQF2X
CMYIE-ODVBK-DR6DB-AN9BC-ZI9AH-TS7BK
CM36Z-CYTBB-OB4XR-QSHVG-26RWV-6FTGU
CMAEZ-4XKJK-4MK2D-ACODL-BEEJO-4N49E
or
Name: mydaj[ROR]
s/n: B4FAA-123D8-31REA-AEOD4-D4R48
[Note: Disconnect from the Internet Before Activation]
Download Link: http://www.tune-up.com/download/
Product key 1:
Use any of these Product Key for TuneUp Utilities 2015 Given Below:
CMETO-2KELO-T39DN-A32EW-FTX2L-FZEZU
CMNPD-UPYJQ-NUQU2-A4BPO-MPWMN-7DRNS
CMEMI-GTISN-W69OO-AMVUG-FM2TI-IPROJ
CMH2P-QXHY6-7HGX9-AFKPM-G2QBX-CZG64
CMGHG-3O24M-BHECP-QP3E4-HHGHR-OOLWW
CMBK3-6EKE6-ZC22B-AQE3D-AKXRG-R6AWP
CMHDF-TCPN7-V2P4E-QRF42-GD4TT-F9C9Q
CM2S6-7JX7V-I3MGR-Q27AM-3SBKV-AW7ZV
CMETO-2KELO-T39DN-A32EW-FTX2L-FZEZU
CMKRU-MS4LL-R7QNG-AGCCY-LR9SS-F6GIW
CM3G6-DR2R3-QOWZW-ATUEF-2GHSE-IQF2X
CMYIE-ODVBK-DR6DB-AN9BC-ZI9AH-TS7BK
CM36Z-CYTBB-OB4XR-QSHVG-26RWV-6FTGU
CMAEZ-4XKJK-4MK2D-ACODL-BEEJO-4N49E
or
Name: mydaj[ROR]
s/n: B4FAA-123D8-31REA-AEOD4-D4R48
[Note: Disconnect from the Internet Before Activation]
0
-Robotically Detect Out-of-date Drivers
2.4 Pro:
Version 2.1
Key:
Version 2.0
Key: 2EC72-368A4-5E4E9-D54A1
Version 1.6
Key: A3DDC-13AD6-C8B24-85CB9
Version 1.5
Key: A3DDC-13AD6-C8B24-85CB9
Version 1.4 Pro
Key: D2B02-DD3B0-6EF1A-8A1B9
Version 1.3
Key: C71DE-50EC8-6AFA0-D20B9
Version 1.2
Version 1.1
Key: 7E6CA-C22FD-0F079-5A0A1
Version 1.0
Key: 2EC72-368A4-5E4E9-D54A1
Disconnect from the internet before you activate it.
read more
Driver Booster 3.0 Beta License Code
Features:
 |
| Driver Booster Beta 3.0 |
-Robotically Detect Out-of-date Drivers
-One-click Update for max Hardware Performance
-Specialized Driver Tweaking for Maximum Gaming Capability
-Fast, Safe and Easy to Use
-Boosts your Desktop/laptop performance
What's New in Version V 3.0:
- Supported 13,000+ drivers & devices
- Detected missing & faulty Drivers
- Better and faster driver download experience
- Automatic driver-backup
- Peak gaming performance
Official Link:
http://www.iobit.com/en/beta/db3/downloadb.php
Driver Booster Beta 3.0 Beta Download link:
https://tusfiles.net/vazghoapavrsDriver Booster 3.0 Beta License Code:
Version 3.0 Beta:
2EC72-368A4-5E4E9-D54A1
Disconnect From the Internet Before Activation.
[If Licensed Period is over then Activate again with the same key]
Old Version :
2.4 Pro:
2EC72-368A4-5E4E9-D54A1
Version 2.1
Key:
2EC72-368A4-5E4E9-D54A1
Version 2.0
Key: 2EC72-368A4-5E4E9-D54A1
Version 1.6
Key: A3DDC-13AD6-C8B24-85CB9
Version 1.5
Key: A3DDC-13AD6-C8B24-85CB9
Version 1.4 Pro
Key: D2B02-DD3B0-6EF1A-8A1B9
Version 1.3
Version 1.2
Key: 2EC72-368A4-5E4E9-D54A1
Version 1.2 Pro
Key: 0B635-E0AA7-970C1-A5BB9 Version 1.1
Key: 7E6CA-C22FD-0F079-5A0A1
Version 1.0
Key: 2EC72-368A4-5E4E9-D54A1
 |
| Activated 3.0 Beta |
Disconnect from the internet before you activate it.
0
If you don't know how to use حr@حk, then follow this post:
[NOTE: If IDM disturbs you by their "Fake Serial Key" massage, then follow this post:
How to stop Fake Serial Key Massage ]
If you don't know how to manually refresh dead link in IDM then follow this post:
How To Manually Refresh Dead Link in IDM
read more
Internet Download Manager (IDM) 6.25 Build 1 [Fake Serial Fixed]
Version 6.25 Final. Released: Oct/08/2015 What's new in version 6.25?
- Improved IDM download engine
- Added support for SeaMonkey 2.38
- Fixed bugs
- Added support for SeaMonkey 2.38
- Fixed bugs
A Complete Guide to Activate IDM full Version
[NOTE: If IDM disturbs you by their "Fake Serial Key" massage, then follow this post:
How to stop Fake Serial Key Massage ]
If you don't know how to manually refresh dead link in IDM then follow this post:
How To Manually Refresh Dead Link in IDM
0

Grand Theft Auto V
Grand Theft Auto V is another installment in one of the most popular series in the history of video games. The game was released initially on Xbox 360 and PlayStation 3 in 2013. Version for computers is an expanded and improved edition of the original title. It offers full support for high screen resolutions. Textures and three-dimensional models are in higher quality. The game world is more living thanks to increased number of cars in traffic and pedestrians. Lighting system, car damages and weather also received improvements. There are also new missions, weapons, vehicles and options of characters customization. Developers had in mind players who earlier bought GTA V for PlayStation 3 or Xbox 360 – they can transfer their characters from GTA Online on console to PC version of the game.
Grand Theft Auto V presents you three completely different characters: Michael – a former bank robber from the East Coast, now being under the witness protection program; Trevor – retired military pilot suffering from mental disorders; and Franklin – young man from the ghetto, collecting cars from debtors of a local Armenian dealer. Each of them represents other social background, presented in the game in a detailed manner. The storyline and gameplay enable switching between those three characters at any time, so you can quickly explore the world of Los Santos and always be in the center of the action.
Features
Direct Download Link



Requirements
read more
Grand Theft Auto V PC Game Repack, Cheats & SaveGame are Here ! [WORKING DIRECT LINKS]
Grand Theft Auto V
Grand Theft Auto V is another installment in one of the most popular series in the history of video games. The game was released initially on Xbox 360 and PlayStation 3 in 2013. Version for computers is an expanded and improved edition of the original title. It offers full support for high screen resolutions. Textures and three-dimensional models are in higher quality. The game world is more living thanks to increased number of cars in traffic and pedestrians. Lighting system, car damages and weather also received improvements. There are also new missions, weapons, vehicles and options of characters customization. Developers had in mind players who earlier bought GTA V for PlayStation 3 or Xbox 360 – they can transfer their characters from GTA Online on console to PC version of the game.
Grand Theft Auto V presents you three completely different characters: Michael – a former bank robber from the East Coast, now being under the witness protection program; Trevor – retired military pilot suffering from mental disorders; and Franklin – young man from the ghetto, collecting cars from debtors of a local Armenian dealer. Each of them represents other social background, presented in the game in a detailed manner. The storyline and gameplay enable switching between those three characters at any time, so you can quickly explore the world of Los Santos and always be in the center of the action.
Features
- Major visual and technical upgrades to make Los Santos and Blaine County more immersive than ever.
- Increased Draw Distances
- 4K Support
- New weapons, vehicles and activities
- Additional wildlife
- Denser traffic
- New foliage system
- Enhanced damage and weather effects, and much more.
Direct Download Link
- Version of the game – 1.0.350.2 (Update 5)
- Do not cut / recoded
- DLC Exclusive Unlocker –
- Installation Time: 4 hours
- Made on popular demand for Pirates.
- Maintained registry and Crack all the way.
- Repack by RG Mechanics.
- Download and Extract the zip file
- Run Setup.exe
- Follow on-screen Instructions
- Wait For Game To Be Installed
- Done, Enjoy
- Download and Mount GTA V DVD 1 and GTA V DVD 2
- Go in GTA V DVD 1 and Open Setup.exe
- Follow On-screen Instructions to Install
- Go Here For Crack
- Copy the crack in GTA V Installation Directory
- Done, Enjoy
Requirements
MinimumNew Downloads (Black Box Repack – 36 GB)
Adjusted
- Core 2 Quad Q6600 2.4GHz
- Phenom 9850 Quad-Core Black Edition
- GeForce 9800 GT
- Radeon HD 4870
- 4 GB Ram
- Windows 7 – 64BIT
- DirectX 10
- 65 GB HDD Space
Recommended
- Core i5-680 3.6GHz
- Phenom II X4 810
- GeForce GTX 750
- Radeon R7 260X v2
- 6 GB Ram
- Windows 7 – 64BIT
- DirectX 11
- 65 GB HDD Space
- Core i5-3470 3.2GHz
- FX 8350
- GeForce GTX 660
- Radeon HD 7870
- 8 GB Ram
- Windows 7 – 64BIT or Higher
- DirectX 11
- 65 GB HDD Space
Direct Link (splitted parts) : Show LinksNon Repacked Retail Download (Original Game – 60 GB)
Torrent : Download Torrent / Magnet
Torrent : Download Torrent / Magnet
0
read more
Clash of Clans Unlimited Mod/Hack v7.200.19 APKs! [ULTIMATE]
Changelog
- 15/10/2014 : Servers are given custom names(beta). Memory leaks and some bugs fixed.
- 21/10/2014 : Multiple servers sharing same database, so that another server can be used, when one is down, and your game progress remains saved, even after changing server.
- 27/10/2014 : New custom server working with latest version
- 29/10/2014 : Custom APK provided with Main Database working on multiple servers.
- 11/11/2014 : New servers
- 12/11/2014 : New Custom APK
- 17/11/2014 : Patched to work with latest version of CoC (Android and ioS)
- 19/11/2014 : Assigned Elastic IP to the main server
- 03/12/2014 : ♪Custom Barbarian Tower and SnowFall added. Its Christmas!! ♥
- 06/12/2014 : All Savings related issues fixed. PvE added! Chasethose Goblins!
- 25/12/2014 : Universal APK released!
- 04/01/2015 : “Dual Install”> You can install both original apk and mod apk on phone! Py side.!
- 23/01/2015 : Bringing you townhall 11!
- 09/03/2015 : PvP added! Enjoy Looting others
- 11/05/2015 : Bugs Fixed
- 09/06/2015 : Tri-servers Introduced
- 27/07/2015 : Clans Introduced! Thunderbolt APK released!
- 23/08/2015: Fixed App not Installed Issue in Lollipop Devices
- 01/10/2015: New version Apk! Tons of bug fixes!
- 27/10/2015: Ultimate Apks! Two different variants! Lollipop users too!
0

Piriform CCleaner
CCleaner is the number-one tool for cleaning your Windows PC. It protects your privacy online and makes your computer faster and more secure. Easy to use and a small, fast download. Piriform releases regular updates for CCleaner with many improvements.
See Also
Screenshots
Serial Keys
read more
CCleaner Any Version PRO Serial Keys are Here !
Piriform CCleaner
CCleaner is the number-one tool for cleaning your Windows PC. It protects your privacy online and makes your computer faster and more secure. Easy to use and a small, fast download. Piriform releases regular updates for CCleaner with many improvements.
See Also
Defraggler Any Version PRO Serial KeysHow to Activate ?
Recuva Any Version PRO Serial Keys
Speccy Any Version PRO Serial Keys
- Download and install the Latest Free Version of CCleaner
- Turn off your Internet Connection (This is important,otherwise keys will not work)
- Launch CCleaner
- Go to Options > About and Click Upgrade to PRO button
- Enter your name and a serial key given below
- Click Register and You’re Done
Screenshots
Serial Keys
C2YW-IAHG-ZU62-INZQ-WZPC
C2YW-2BAM-ADC2-89RV-YZPC
C2YW-XFCX-ABIG-GZD4-8ZPC
C2YW-XK32-GBVV-N3BH-2ZPC
C2YW-JKW5-KK79-XHR2-4ZPC
C2YW-QTRT-ZVCG-PQDK-CZPC
C2YW-GP33-TPIU-BGM8-AZPC
DownloadsTuesday, 3 November 2015
0
Tuesday, 3 November 2015

In the recent hack at Ashley Madison revealed an uncommon thing, people used very easy to crack passwords at the most coveted site to cheat partners.
All those accounts that got hacked at Ashley Madison used such easy and convenient to them. Those Passwords are so easy that entire internet can rate them as top 100 easiest passwords that people used on internet.
Some examples are 123456, 12345 and Password as password.
We have a list of passwords and the times they have been used by users according to the CynoSure Prime account
The researchers have strategized the entire data into subsets of 15 million accounts that uses a single form and can be encrypted with an ease at the stipulated time.
First they focused on the simpler ones and then they are increasing their complexity level to encrypt passwords.
The most common pattern found on this website for keeping password is depicted below.
Only Lowercase passwords were used by 4912306 users
Lowercase with numbers were used by 4395724
Numbers Only 1406878
Lowercase and uppercase used by 193143
Passwords that include special character were used by 92991
There is a list of some passwords that could not make it to top 100 but are noteworthy.
read more
Ashley Madison top 100 are the easiest passwords that existed on internet
In the recent hack at Ashley Madison revealed an uncommon thing, people used very easy to crack passwords at the most coveted site to cheat partners.
All those accounts that got hacked at Ashley Madison used such easy and convenient to them. Those Passwords are so easy that entire internet can rate them as top 100 easiest passwords that people used on internet.
Some examples are 123456, 12345 and Password as password.
We have a list of passwords and the times they have been used by users according to the CynoSure Prime account
The researchers have strategized the entire data into subsets of 15 million accounts that uses a single form and can be encrypted with an ease at the stipulated time.
First they focused on the simpler ones and then they are increasing their complexity level to encrypt passwords.
The most common pattern found on this website for keeping password is depicted below.
Only Lowercase passwords were used by 4912306 users
Lowercase with numbers were used by 4395724
Numbers Only 1406878
Lowercase and uppercase used by 193143
Passwords that include special character were used by 92991
There is a list of some passwords that could not make it to top 100 but are noteworthy.
- ishouldnotbedoingthis
- ithinkilovemywife
- thisiswrong
- whatthehellamidoing
- whyareyoudoingthis
- cheatersneverprosper
- donteventhinkaboutit
- isthisreallyhappening
0

On Wednesday IOS devices received an update with version 9.0.1 where the update still failed to solve the various bugs in the system. The very famous of all is the lock screen bypass. This bypass is the major vulnerability in iOS these days. This was reported first by an iPhone user Jose Rodriguez.
This flaw or vulnerability talks about the permission or grant of access to your iPhone or iPad through physical access. This bypass can provide access to hacker and it can provide contacts and personal photographs through physical touch.
Rodriguez also posted a video in which a detailed explanation is provided to users with a structure and step by step process. The entire process is depicted using Siri as well which is Apple’s personal assistant. The video focused on the bypass vulnerability to be accessed on all the versions of iOS 5.1.1 to the latest release IOS 9.0.1
The one way through which Apple can overcome this serious flaw or vulnerability is to update a patch for this bug. The best and most secure way is to deactivate Siri from being accessed from the lock screen to safeguard phone.
How you can disable Siri
Go to Settings
Click on Touch Id and passcode options
Enter your passcode in the prompt box that appears.
Look out for option “allow access when locked” and choose disable Siri.
This bug is much smaller to one of the bugs in Android Lollipop which got fixed lately. The Android lock bypass was more difficult than iOS to patch with the most dangerous impact.
The most harmful aspect is this android lock provides bypass which attackers use to steal away important files as well as that can install the apps that are malicious in the affected device. The entire week was sad for Apple’s iOS security as they figured out 4000 malware infested applications on the app store.
read more
Bypass Hack still not resolved by the latest IOS update 9.0.1
On Wednesday IOS devices received an update with version 9.0.1 where the update still failed to solve the various bugs in the system. The very famous of all is the lock screen bypass. This bypass is the major vulnerability in iOS these days. This was reported first by an iPhone user Jose Rodriguez.
This flaw or vulnerability talks about the permission or grant of access to your iPhone or iPad through physical access. This bypass can provide access to hacker and it can provide contacts and personal photographs through physical touch.
Rodriguez also posted a video in which a detailed explanation is provided to users with a structure and step by step process. The entire process is depicted using Siri as well which is Apple’s personal assistant. The video focused on the bypass vulnerability to be accessed on all the versions of iOS 5.1.1 to the latest release IOS 9.0.1
The one way through which Apple can overcome this serious flaw or vulnerability is to update a patch for this bug. The best and most secure way is to deactivate Siri from being accessed from the lock screen to safeguard phone.
How you can disable Siri
Go to Settings
Click on Touch Id and passcode options
Enter your passcode in the prompt box that appears.
Look out for option “allow access when locked” and choose disable Siri.
This bug is much smaller to one of the bugs in Android Lollipop which got fixed lately. The Android lock bypass was more difficult than iOS to patch with the most dangerous impact.
The most harmful aspect is this android lock provides bypass which attackers use to steal away important files as well as that can install the apps that are malicious in the affected device. The entire week was sad for Apple’s iOS security as they figured out 4000 malware infested applications on the app store.
0

Have you ever witnessed your phone making different calls send text messages and internet browsing without your permission and authentication?
It might be possible that a hacker hacked your phone and using your phone in fact your personal assistant Siri or may be Google Now.
This is the latest hack in the market that give permission to hackers through which they can make calls, send text browse infected sites and other activities that are harmful for your android and IOS device. The most amazing is use of google now or Siri without even uttering a word, they will be able to use it as per researched by Internet Researchers.
NSSI’s group of researchers who belong to French government have revealed that hacker can control any android or IOS device remotely by sending radio commands from 16 feet distance.
Know how this Hack works lets unveil the secret.
The very basic and foremost important thing required is the IPhone or Android phone must have headphones plugged in with a radio transmitter.
The radio waves are used for this hack and the waves initiate voice commands on any iPhone and Android phone that has a microphone enabled headphones plugged in.
Headphones are the one who help in transmitting radio as the headphones has radio antennas. The headphones are treated as radio antennas and can be exploited by hackers that can lead to user’s permission.
This will enable a hacker to use your entire phone without even talking to the user of phone. The permission list includes
Making calls
Send text messages
Dial hacker’s number turn on the phone’s eavesdropping device.
Browsing of malware websites
Phishing and spam messages using social channels
One can send some electromagnetic waves that can call a paid number and get cash.
The hack only needs:
read more
New Hack On The Block With Siri and Google Now!
Have you ever witnessed your phone making different calls send text messages and internet browsing without your permission and authentication?
It might be possible that a hacker hacked your phone and using your phone in fact your personal assistant Siri or may be Google Now.
This is the latest hack in the market that give permission to hackers through which they can make calls, send text browse infected sites and other activities that are harmful for your android and IOS device. The most amazing is use of google now or Siri without even uttering a word, they will be able to use it as per researched by Internet Researchers.
NSSI’s group of researchers who belong to French government have revealed that hacker can control any android or IOS device remotely by sending radio commands from 16 feet distance.
Know how this Hack works lets unveil the secret.
The very basic and foremost important thing required is the IPhone or Android phone must have headphones plugged in with a radio transmitter.
The radio waves are used for this hack and the waves initiate voice commands on any iPhone and Android phone that has a microphone enabled headphones plugged in.
Headphones are the one who help in transmitting radio as the headphones has radio antennas. The headphones are treated as radio antennas and can be exploited by hackers that can lead to user’s permission.
This will enable a hacker to use your entire phone without even talking to the user of phone. The permission list includes
Making calls
Send text messages
Dial hacker’s number turn on the phone’s eavesdropping device.
Browsing of malware websites
Phishing and spam messages using social channels
One can send some electromagnetic waves that can call a paid number and get cash.
The hack only needs:
- A headphone-linked iPhone or Android phone
- Siri enabled from the lock screen as a Apple’s Default setting.
0
Feed limitation alert
Hi,
You reached your feed limit. Please either remove number of feeds to equal current plan or upgrade your plan.
For plan upgradation: Click here
Manage your feed: Click here
Thanks,
FeedMyInbox Team
read more
You reached your feed limit. Please either remove number of feeds to equal current plan or upgrade your plan.
For plan upgradation: Click here
Manage your feed: Click here
Thanks,
FeedMyInbox Team
0
Welcome to feedMyInbox
Hi s.haidersoft.mm44@blogger.com
Thanks for registering with us.
For email confirmation:
Click here
Thanks,
FeedMyInbox Team
read more
Thanks for registering with us.
For email confirmation:
Click here
Thanks,
FeedMyInbox Team
0
Confirm Subscription Link
Hi,
Thanks for subscribing http://www.tech.com.pk/feed.
Please click on below link to confirm this feed :
Click here
Thanks,
FeedMyInbox Team
read more
Thanks for subscribing http://www.tech.com.pk/feed.
Please click on below link to confirm this feed :
Click here
Thanks,
FeedMyInbox Team
Monday, 8 June 2015
0
Monday, 8 June 2015
read more
Snake Game written in JAVA (Full Source Code)
In this article, I'll re-write a simplified version of the very famous game "Snake" in JAVA programming language. You can easily find dozens of similar source code by googling around, however, a majority of them are far from being simple that the game requires, containing complex scripts and hard to read and to understand. Especially, the examples in JAVA are written by unskilled programmers who are anaware of what Object Oriented Programming is ... (more)
In this article, I'll try to make the source code easily readable and understandable by dividing the whole code into small JAVA classes and by using the flexibility that JAVA provides. At the end of this article, the overall appearance of our project will be as follows:
Now, we can start writing our classes. Let's name our first class Cell.java:
In this article, I'll try to make the source code easily readable and understandable by dividing the whole code into small JAVA classes and by using the flexibility that JAVA provides. At the end of this article, the overall appearance of our project will be as follows:
Subscribe to:
Posts (Atom)